Snowflake Data masking at column level is of special interest in tables and views at the time of query due to the way it covers plain-text data using masking strategies. This article covers the overview of snowflake dataset masking. Continue reading to learn more about snowflake data masking.
Items at the blueprint level are snowflake data masking approaches. Therefore, masking strategies are not possible without a database, and mapping must exist in Snowflake before the strategy can be applied. The current version of Snowflake allows tables and perspectives to utilize Snowflake Data Masking.
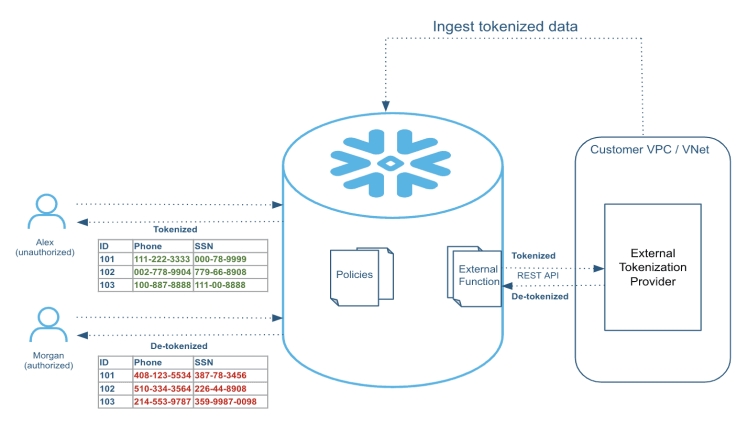
The data masking strategy is applied to a section during runtime at each location where the segment is to be displayed. In Snowflake data masking, the value may be displayed as plain text, partially concealed, or completely hidden, depending on the masking strategy and the SQL execution setting.
Understanding Column-level Security provides further insight into masking arrangements, including the question runtime process, creating a strategy, utilizing tables and perspectives, and the way the board employs masking strategies.
Snowflake Data Masking Offers Benefits
In the following, we’ve outlined a portion of Snowflake Data Masking‘s important benefits. Keep scrutinizing to find out about them.
A User-friendly Interface
A snowflake data masking can be composed once, and it can be applied across many sections in databases and outline documents.
Organizing Data And Establishing An Information System
Article owners cannot decide which sections do or do not need to be examined by security or protection officials. Making approaches are relatively easy to maintain and oversee with an incorporated and decentralized organizational structure.
Administration And Approval Of Data
Job-related and custom privileges for accessing relevant data. Provides data administration support for security and protection personnel, as well as the option to restrict the access to data by special clients with the ACCOUNTADMIN or SECURITYADMIN jobs.
Sharing Of Data Through Collaboration
Sharing of data can be made more secure by hiding it first. There needs to be a change in the executive team. An effective masking strategy can be modified to suit various situations rather than having to reapply on numerous occasions.
Creating A Snowflake Data Masking
In this post, we record the undeniable steps that Snowflake Data Masking users should take to appropriately arrange and utilize it:
- A marketing strategy that emphasizes a product’s advantages for a custom job for a protection or security official.
- As a security and protection official, the official creates and characterizes snowflake data masking strategies used by security and protection officials during sensitive operations.
The Snowflake application is used for executing questions. The accompanying paragraph describes what should be done:
A group of Snowflakes, using the masking strategy SQL articulation, develops the question incrementally. In the data analysis, revision occurs where the section indicated in the snowflake data masking strategy appears, as in projections, joins, where clauses, requests, and bunches. Data covered by a Snowflake data masking approach depends on the implementation setting conditions described by the approaches.